Boost Your Information Safety With Reliable Cloud Storage Solutions
Enhancing information protection via trusted cloud storage space solutions is a critical aspect of contemporary service operations. As cyber risks continue to evolve, companies must focus on guarding their delicate details. By leveraging safe and secure cloud storage remedies, services can fortify their defenses versus information breaches and unauthorized accessibility. The sophisticated safety and security attributes offered by reliable cloud suppliers not just safeguard information at rest and en route but likewise guarantee business continuity and regulatory conformity. Remain tuned to discover just how cloud storage solutions can elevate your data protection methods and alleviate possible threats efficiently.
Significance of Information Protection
Why is information safety important in today's digital landscape? The raising reliance on electronic platforms for keeping and handling delicate information has actually made information protection much more crucial than ever previously. With cyber dangers ending up being a lot more sophisticated and widespread, ensuring the security of information has actually become a top concern for organizations and individuals alike. Information breaches can have extreme consequences, including monetary loss, damages to online reputation, and lawful effects. Consequently, executing durable data safety and security procedures is vital to safeguarding versus prospective risks.
Information safety assists avoid unauthorized access, disclosure, alteration, or destruction of data, guaranteeing that it remains protected and protected from harmful stars. By adopting best techniques and leveraging sophisticated modern technologies, such as encryption and access controls, organizations can boost their information safety and security posture and minimize the likelihood of information violations.
Advantages of Cloud Storage
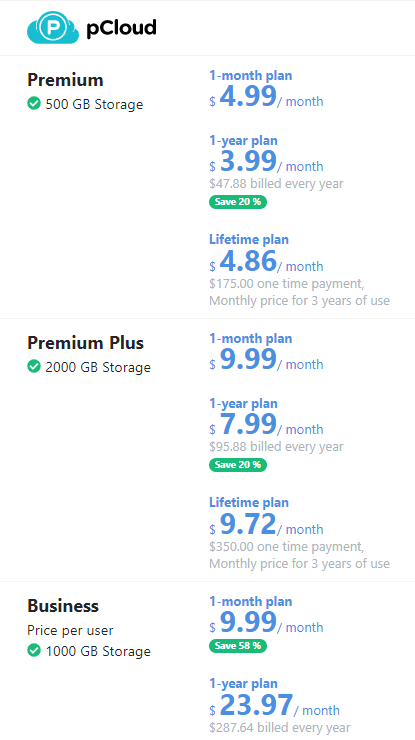
In today's data-driven landscape, cloud storage solutions provide a multitude of advantages that boost information safety and ease of access for businesses and individuals alike. One vital advantage of cloud storage space is its scalability. Individuals can quickly change their storage requires, whether raising or lowering capability, without the need for physical hardware upgrades. This adaptability not just conserves prices but likewise guarantees that information storage space aligns with current requirements.
Another advantage is the boosted data safety includes given by trustworthy cloud storage carriers. These services typically offer file encryption, information redundancy, and regular backups to safeguard data from violations, loss, or corruption. Furthermore, cloud storage enables seamless partnership amongst individuals, allowing real-time accessibility to data from anywhere with a web connection. This function increases performance and effectiveness within groups, specifically in remote job setups. Furthermore, cloud storage solutions usually come with automated syncing abilities, making certain that the latest variations of data are always obtainable and up to date.
Variables for Selecting Supplier
Another vital variable is the level of information encryption and safety measures used by the company. Make sure that the cloud storage space service applies robust file encryption protocols to guard your data both en route and at rest. Scalability and flexibility are likewise essential considerations when choosing a supplier. Your company's storage demands may transform in time, so pick a copyright that can suit your progressing needs without compromising information security. Evaluate the copyright's information backup and calamity recovery capabilities to ensure that your top article data continues to be accessible and protected in the event of any unpredicted incidents.
File Encryption and Data Defense
Making certain durable file encryption procedures and rigid data defense actions is crucial when turning over delicate details to cloud storage services. Security plays an important function in safeguarding data both in transit and at remainder within the cloud setting. universal cloud Service. By encrypting information, info is transformed right into a safe and secure layout that can only be accessed with the suitable decryption trick. This assists prevent unapproved access to Related Site confidential information, ensuring its confidentiality and honesty.
Safety And Security Best Practices
Executing durable protection ideal techniques is vital in guarding information integrity and discretion within cloud storage services. One essential finest method is making certain solid accessibility controls. This entails enforcing strict verification procedures such as multi-factor authentication, solid password policies, and normal accessibility reviews to stop unapproved entry into the system. In addition, routine protection audits and susceptability evaluations are vital to recognize and fix any type of possible weaknesses in the cloud storage environment.
An additional vital safety ideal practice is information file encryption both en route and at rest. If obstructed throughout transmission or storage space, using security procedures ensures that data continues to be safe even. It is also advisable to apply automatic backup and calamity recuperation treatments to guard against data loss because of unanticipated occasions like cyberattacks or system failures.
In addition, keeping up-to-date safety and security patches and remaining educated concerning the most recent protection dangers and fads are vital for positive security monitoring. Education and training for employees on protection methods and best methods additionally play an essential duty in strengthening the total security stance of cloud storage services. By adhering to these safety best methods, companies can enhance the security of their sensitive data saved in the cloud.
Final Thought
In verdict, reliable cloud storage services supply a safe and reliable option for protecting your information. With sophisticated file encryption, information redundancy, and regular back-ups, these services guarantee the discretion, honesty, and schedule of your info. By carefully picking a reliable supplier and adhering to safety ideal methods, you can boost your overall information security posture and safeguard your beneficial data from prospective cyber get more risks.
Data security helps prevent unapproved access, disclosure, alteration, or damage of information, ensuring that it stays safe and secure and safeguarded from harmful stars. By embracing ideal methods and leveraging innovative technologies, such as encryption and access controls, organizations can enhance their data safety stance and reduce the probability of information breaches. These services typically use file encryption, information redundancy, and routine back-ups to secure data from violations, loss, or corruption - universal cloud Service. Evaluate the copyright's information backup and disaster healing capacities to make sure that your data remains available and protected in the occasion of any type of unexpected events
By very carefully adhering to and choosing a reliable supplier safety and security finest practices, you can improve your overall data security posture and secure your important data from prospective cyber dangers.